
In 2021, cybercrime has become more sophisticated, widespread, and relentless. Criminals have targeted critical infrastructure—healthcare,1 information technology,2 financial services,3 energy sectors4—with headline-grabbing attacks that crippled businesses and harmed consumers. But there are positive trends—victims are coming forward, humanizing the toll of cyberattacks and prompting increased engagement from law enforcement. Governments are also passing new laws and allocating more resources as they recognize cybercrime as a threat to national security.
Earlier this month, Microsoft published the 2021 Microsoft Digital Defense Report (MDDR). Drawing upon over 24 trillion daily security signals across the Microsoft cloud, endpoints, and the intelligent edge, the 2021 MDDR expands upon last year’s inaugural report and contains input from more than 8,500 security experts spanning 77 countries—including insights on the evolving state of ransomware, malicious email, malware, and more.
Ransomware goes retail
Ransomware offers a low-investment, high-profit business model that’s irresistible to criminals. What began with single-PC attacks now includes crippling network-wide attacks using multiple extortion methods to target both your data and reputation, all enabled by human intelligence. Through this combination of real-time intelligence and broader criminal tactics, ransomware operators have driven their profits to unprecedented levels.
This human-operated ransomware, also known as “big game ransomware,” involves criminals hunting for large targets that will provide a substantial payday through syndicates and affiliates. Ransomware is becoming a modular system like any other big business, including ransomware as a service (RaaS). With RaaS there isn’t a single individual behind a ransomware attack; rather, there are multiple groups. For example, one threat actor may develop and deploy malware that gives one attacker access to a certain category of victims; whereas, a different actor may merely deploy malware. It’s effectively a crime syndicate where each member is paid for a particular expertise.
Once a criminal actor compromises a network, they may steal confidential information, financial documents, and insurance policies. After analyzing this intelligence, they will demand an “appropriate” ransom to not only unlock their victim’s systems but also to prevent public disclosure of exfiltrated data. This is known as the double extortion model: a victim is extorted for ransom on stolen data and intellectual property (IP), and then again to prevent the attacker from publishing it.
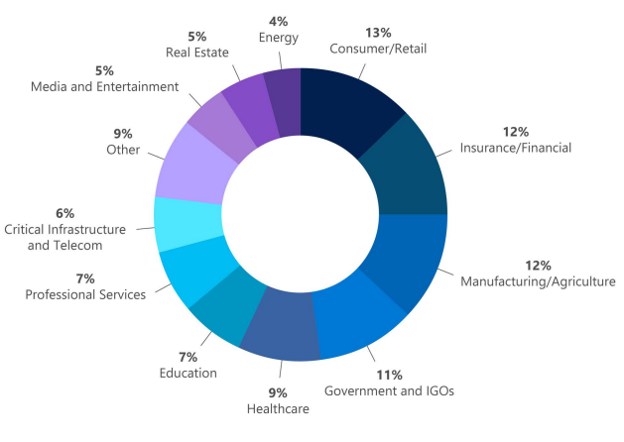
Typically, threat actors will demand payment through cryptocurrency wallets. The underlying blockchain technology enables the owners of crypto wallets to remain pseudonymous. But the criminal actor needs to find a way to cash out, which is where middlemen in the cryptocurrency ecosystem step in to facilitate ransom-related transactions and payments. Both the private sector and government agencies—through civil litigation, prosecution, regulatory enforcement, and international collaboration—can take coordinated action against ransomware intermediaries to disrupt the payment process. Data from Microsoft’s Detection and Response Team (DART) shows that the three sectors most targeted by ransomware were consumer, financial, and manufacturing.
The best way to be prepared against ransomware is to make it harder for attackers to access systems while making it easier for victims to recover—without paying a ransom. Encouraging organizations to prepare for the worst is actually a proactive strategy, one that’s designed to minimize monetary incentives for attackers. To learn more about defending against ransomware, read the 2021 MDDR. Microsoft also supports the guidance presented in the Ransomware Playbook by the Cyber Readiness Institute.

Malicious email: Bait and switch
Reports of phishing attacks doubled in 2020, with credential phishing used in many of the most damaging attacks. The Microsoft Digital Crimes Unit (DCU) has investigated online organized crime networks involved in business email compromise (BEC), finding a broad diversification of how stolen credentials are obtained, verified, and used. Threat actors are increasing their investment in automation and purchasing tools, so they can increase the value of their criminal activities.
Overall, phishing is the most common type of malicious email observed in our threat signals. All industries receive phishing emails, with some verticals more heavily targeted depending on attacker objectives, availability of leaked email addresses, or current events regarding specific sectors and industries. The number of phishing emails we observed in Microsoft Exchange global email flow increased from June 2020 to June 2021, with a pronounced surge in November potentially taking advantage of holiday-themed traffic.
“In 2020, the industry saw a surge of phishing campaigns that has remained steady throughout 2021. Internally at Microsoft, we saw an increase in overall number of phishing emails, a downward trend in emails containing malware, and a rise in voice phishing (or vishing).”—2021 Microsoft Digital Defense Report
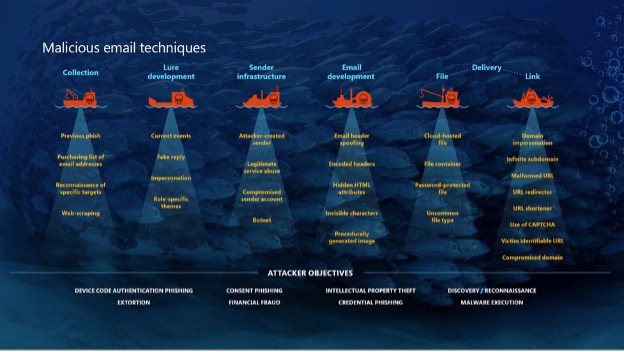
Phishing sites frequently copy well-known, legitimate login pages, such as Microsoft Office 365, to trick users into inputting their credentials. In one recent example, attackers combined open redirector links with bait that impersonates well-known productivity tools and services. Users clicking the link were lead to a series of redirections—including a CAPTCHA verification page that adds a sense of legitimacy—before landing on a fake sign-in page and finally, credential compromise. Those stolen identities can then be weaponized in BEC attacks or via phishing websites. Even after a successful attack, threat actors may re-sell accounts if the credentials remain compromised.
Microsoft Defender SmartScreen detected more than a million unique domains used in web-based phishing attacks in the last year, of which compromised domains represented just over five percent. Those domains typically host phishing attacks on legitimate websites without disrupting any legitimate traffic, so their attack remains hidden as long as possible.
Domains created specifically for attacks tend to be active for shorter periods. Over the last year, Microsoft has seen attacks come in short bursts that begin and end within as little as one to two hours.
Because those minutes matter, Microsoft is again co-sponsoring the annual Terranova Gone Phishing Tournament™, which uses real-world simulations to establish accurate clickthrough statistics. By using a real phishing email template included in Microsoft Defender for Office 365, Attack Simulator provides context-aware simulations and hyper-targeted training to educate employees and measures behavior changes.
Read the full article from Microsoft, here: https://www.microsoft.com/security/blog/2021/10/11/how-cyberattacks-are-changing-according-to-new-microsoft-digital-defense-report/
Phone: (305) 517 1000
Support: (305) 517 1001
Email: [email protected]
LogixCare LLC. 2023 © All Rights Reserved